I had the privilege of being part of an exclusive training event as part of the Veeam Vanguards program. Specifically, one of the first conducted Veeam Backup & Replication v11: Architecture and Design courses. In this post, I will give you an overview of the structure of the course and why I think it is definitely worth your time and money. The second post in this series will focus on the associated exam and will be published once I have taken the exam.
Continue reading „Take your skills to the next level with the Veeam Certified Architect (VMCA 2022) certification – The Training“It’s a wrap! Goodbye 2021, welcome 2022!
This is not the usual technical post you usually find on my blog. Rather, it is a kind of review of the past year 2021. So for those who are interested in technical things and not in private and sentimental stuff: Stop reading after the next paragraph. Everyone else is welcome to read on afterwards.
TL;DR
Whether family, friends, acquaintances, partners, vendors, customers, craftsmen and anyone who does not feel belonging to one of the previously mentioned categories and whom I have therefore forgotten at this point: Thank you for an incredible year 2021, stay healthy and hopefully we will see each other again in 2022!
Continue reading „It’s a wrap! Goodbye 2021, welcome 2022!“Backup job failed Error: DiskLib error: [4].A file error was encountered — Failed to read the file
Lately one of my customers had some issues with his VMware vSphere environment where the semi-outage of one ESXi took down quit a huge amount of his VMs. After fixing the issue in his productive infrastructure and bringing back his IT everything seamed working again. Some days later we noticed Errors in some of his Veeam Backup Jobs. Strangely not all VMs where affected and those affected had no direct correlation (e.g. same ESXi host, same datastore, some network, etc.).
The error message shown inside the Veeam Backup & Replication console was an error I have not seen before:
Error: DiskLib error: [4].A file error was encountered -- Failed to read the file
Error Failed to retrieve next FILE_PUT message. File path: [[<DATASTORE>] <VMFOLDER>/<VM>.vmx]. File pointer: [0]. File size: [3802].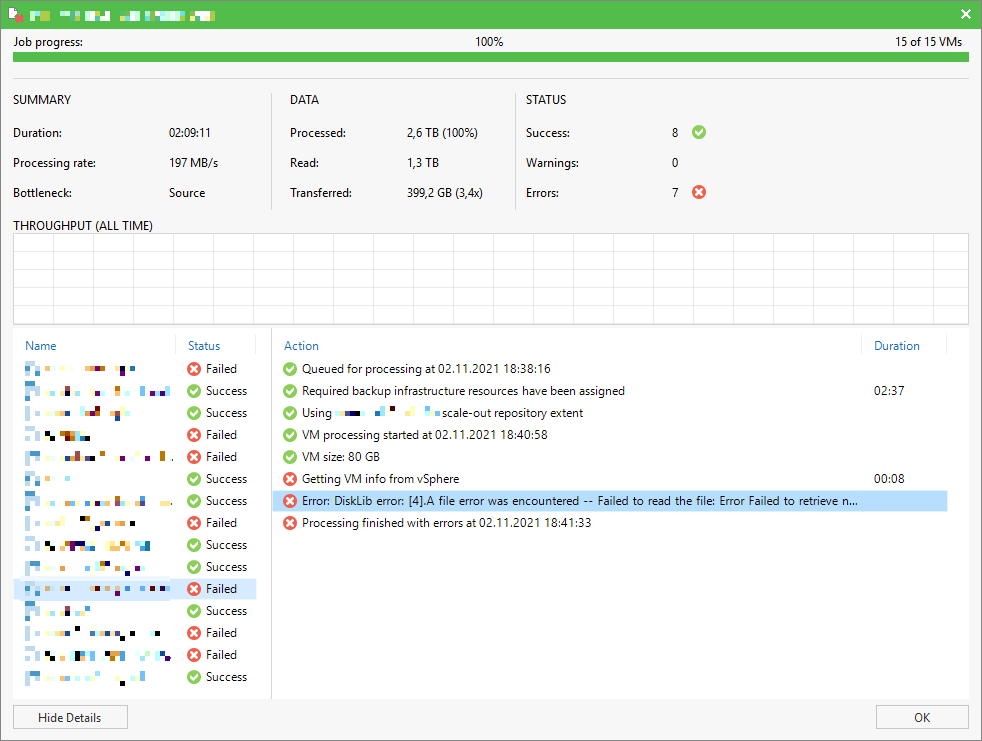
Error Failed to retrieve next FILE_PUT message. File path: [[<DATASTORE>] <VMFOLDER>/<VM>.vmx]. File pointer: [0]. File size: [3802].
My (online proctored) VMCE 2021 experience
Last year I wrote a blog post about my online proctored VMCE 2020 exam experience. Since I took the VMCE 2021 exam a few days ago I do not want to spare you an updated view on my experience associated with the exam. You can find the post about the 2020 exam right here.
Instead of hiding the new badge until the end of the post I am going to tease you with the nice VMCE 2021 Badge right from the start this time.
Continue reading „My (online proctored) VMCE 2021 experience“Create firewall rules for Veeam Backup & Replication server via PowerShell
Today I received a message from a customer asking for a way to restore the firewall rules created during the installation. Somehow he managed to reset the Windows firewall back to default which wiped all custom rules including the Veeam ones.
After doing a little research, I stumbled across a post on the Veeam R&D forum. James Wilmoth (TitaniumCoder477) faced a similar problem and wrote a PowerShell script to recreate the required firewall rules alongside some other custom rules. His script is based on a standard Installation for Veeam Backup & Replication Version 10 and can be found here. Credit for most of the coding work belongs to him!
Even though I had already exported the rules from another installation, I decided against restoring the rules individually and by hand. So I invested some time and created a script for version 11 based on the script for version 10. First the script populates an array with a lot of firewall rules. Find a sample rule definition outlined below.
$rule = @{
DisplayName = "Veeam Backup UI Server (In)";
Description = "Inbound rule for Veeam Backup UI Server";
Group = "Veeam Networking";
Direction = "Inbound";
Profile = "Any";
Enabled = "True";
Action = "Allow";
Program = "C:\Program Files\Veeam\Backup and Replication\Backup\Veeam.Backup.UIServer.exe";
Protocol = "TCP";
LocalPort = "9396";
}
$rules.Add($rule) > $nullAfter filling up the array with all the inbound and outbound firewall rules the individual rules are generated in a loop, using the New-NetFirewallRule cmdlet.
$rules | ForEach-Object {
New-NetFirewallRule @_
}The script is quite fast, runs only for a few seconds and creates all the rules including description etc. You can find the final script in my public VBR GitHub repository right here.
Wrap-Up
I have not written much code lately, so I was happy to take an already existing script as a starting point. Thanks and credit for the code and the logic behind it go, as already mentioned, to James Wilmoth (TitaniumCoder477)!
If you have any suggestions or ideas for improvement, don’t hesitate to contact me.
vSAN 7.0 Update 3 cluster shutdown and restart
Today I demonstrated some of the new features of VMware vSAN 7.0 Update 3 (7.0 U3) related to 2-node deployments to one of our customers who uses this topology extensively. We have focused particularly on improvements to the resilience of 2-node clusters and the witness Host. You can find a short video about the features here. An extensive list of the new features and the release notes can be found here and here.
Another new feature I noticed but forgot zu demonstrate to the customer ist the new vSAN cluster shutdown and restart operation. I already tested the shutdown and restart feature with my 4-node cluster but as the demo was finished I decided to give the feature a try with the 2-node cluster and the external witness appliance.
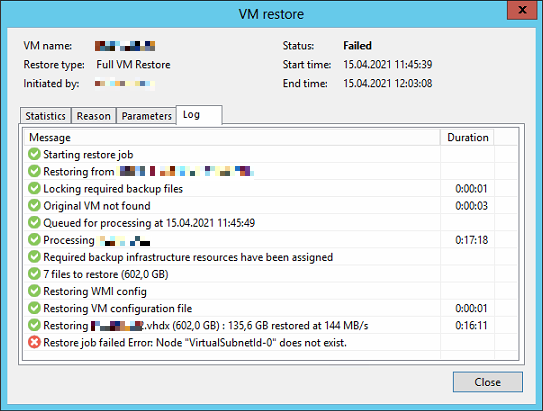
Restore job failed Error: Node “VirtualSubnetId-0″ does not exist
Some time ago I had one of those rare days where I struggled to restore a VM using Veeam Backup & Replication. Some would claim that this has nothing to do with Veeam Backup & Replication, but is solely due to the choice of hypervisor. At this point, I would neither agree nor disagree with this claim, but there is definitely a reason why VMware is ahead in the field of server virtualization.
Actually, the whole thing should have been a fairly simple undertaking: Restore a complete VM to a specific point in time. At first everything looked fine, but after the virtual disks were restored and the VM should have started, the fun began.
VeeamON 2021 – Registration open
Registration for Veeam’s annual vendor exhibition has been open for a few days. Once again this year, VeeamON will take place as a free virtual conference. So register today and enjoy great presentations by various Veeam experts. Not only will you benefit from your registration, but for every registration Veeam will donate $3 to the Girls Who Code (@GirlsWhoCode) initiative.
As a little goodie you have the opportunity to receive a Veeam Swag Box when registering until April 22nd. So don’t wait too long, register today and we’ll see each other at #VeeamON 2021!
Migration options for a VM are greyed out
Every year, before Christmas, the update window is coming up for some of my customers. One of these customers was due for minor VMware vSphere updates today. Actually not a big deal even if the customer has not activated vSphere Distributed Resource Scheduler (DRS) on his cluster due to missing licenses. As in previous years, the task was to manually evacuate the individual ESXi hosts one by one and then standardize them via the vSphere Update Manager (VUM). At the beginning everything was running without any issues until I wanted to evacuate the vCenter Server Appliance (VCSA) as the last VM of the host. For whatever reason, the migrate function was grayed out in the context menu of the VM.
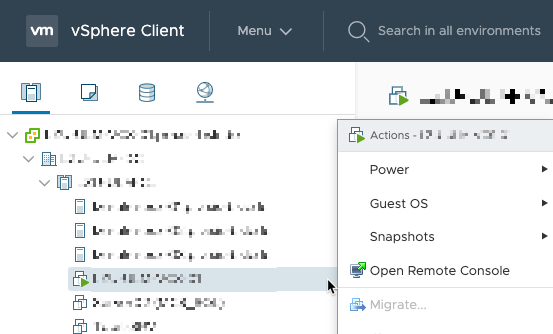
So far, vMotion has actually never caused any problems in this cluster. So it was once again time for a little round of troubleshooting.
Continue reading „Migration options for a VM are greyed out“Networking problems after starting a Advanced Multi-Host Virtual Lab in Veeam Backup & Replication
Today’s Homelab session dealt with the creation of a short customer demo of the Veeam Backup & Replication functionality SureBackup. As I have already implemented several SureBackup jobs for other customers, I was confident that I could quickly finish configuring the environment. For those who have not worked with SureBackup before, Veeam provides an excellent guide in their Help Center. You can find this guide here. Unfortunately the whole thing did not work out as expected. Already at the beginning I made a crucial mistake which made the creation of the demo a nerve-wracking adventure. More on this in a moment. First of all, for those of you who have no idea how the creation of a SureBackup job works, I would like to give a short outline.
Continue reading „Networking problems after starting a Advanced Multi-Host Virtual Lab in Veeam Backup & Replication“
